VIII. Annex (downloads)
8.1. Annex
Structures / manning
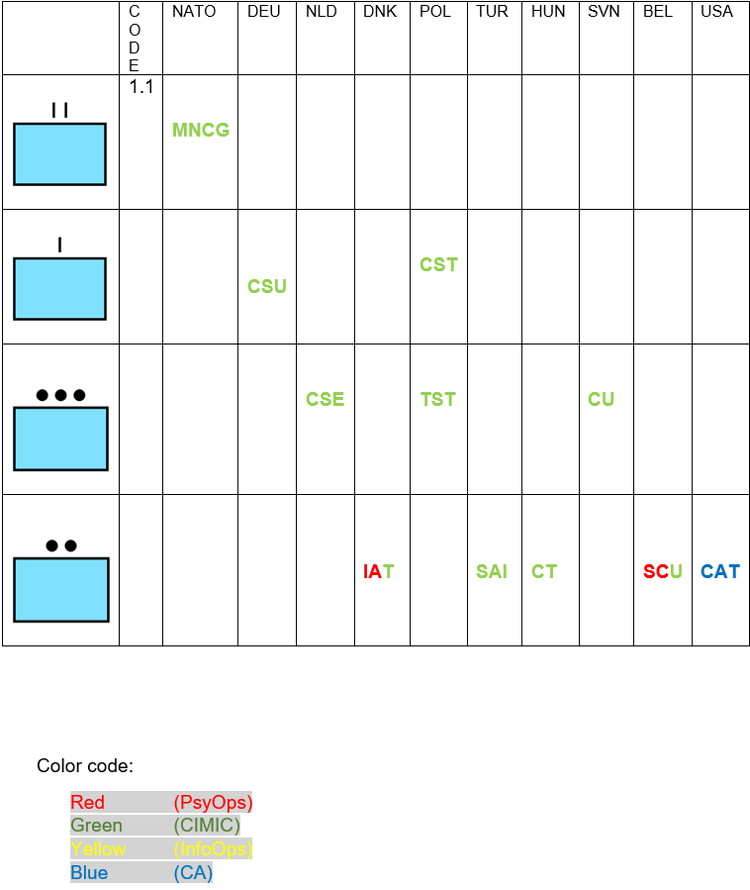
Common understanding of CIMIC teams.
Abbreviation:
EU BG:
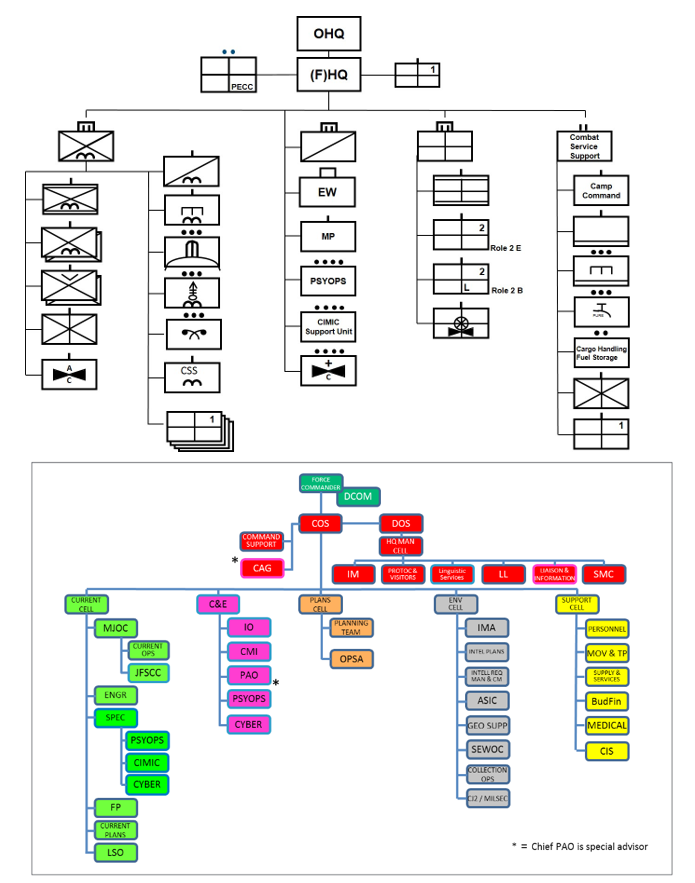
Composition, structure, manning CJ9 of an EU (F) HQ for an EU BG (example):
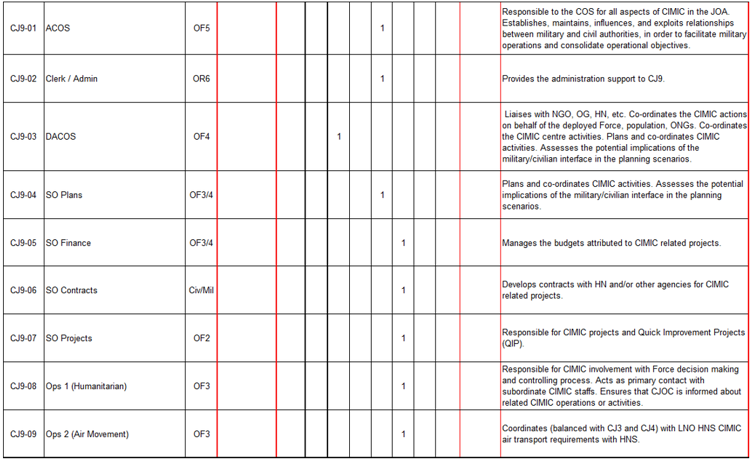
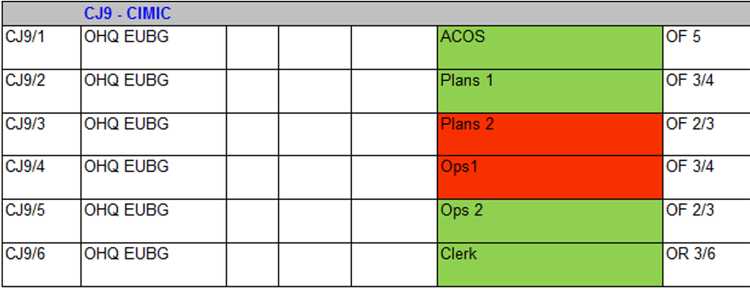
Composition, structure, manning CJ9 of an EU OHQ (example):
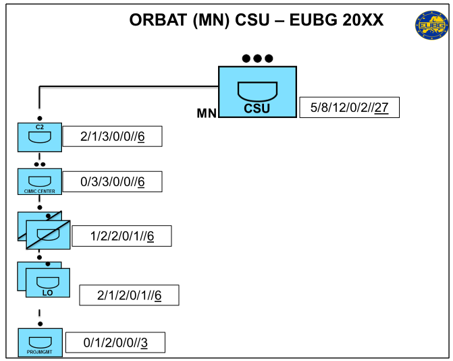
Example for a CIMIC unit within an EU BG:
Non-military actors

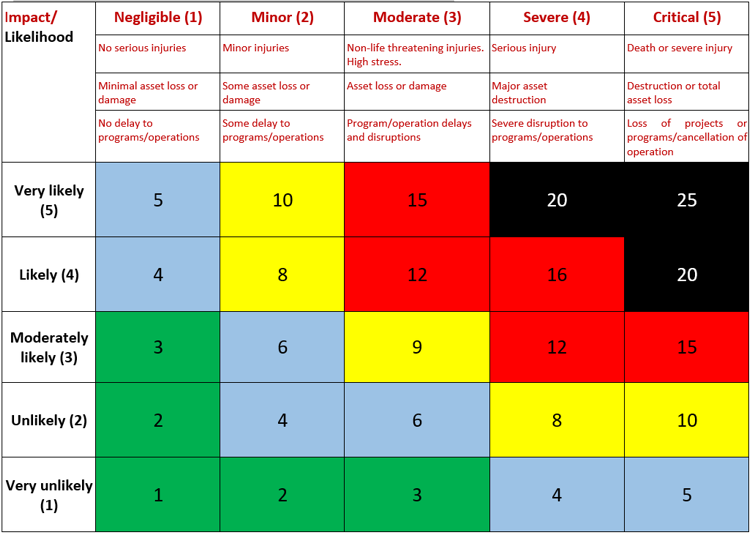
Risk Analysis
Risk Analysis is a proven way of identifying and assessing factors that could negatively affect the success of an operation or a project. It allows to examine the potential risks and helps to decide whether or not to move forward with a decision.
Risk Analysis triggers the following bullets:
- likelihood of a threat
- and impact on the operation or further procedures.
Resulting in a Net Risk-matrix, introducing to the threat-level overall.
When the value of the risks is worked out, next step would be to start looking at ways to manage them effectively and mitigate the risks.
Identify Threats
The first step in Risk Analysis is to identify the existing and possible threats in the operating theatre. These can come from many different sources and is not limited to the sources listed:
- Political - new government after election, Turnoil, change of stakeholders, change in public opinion
- Economy: collapse of the market system,
- Reputational – Loss of confidence against stakeholders, or damage reputation.
- Human – Illness, death, injury, or other loss of a key individual.
- Operational – Disruption to support operations, loss of access to essential assets
- Procedural – Failures of accountability, internal systems, or controls, or from fraud etc..
- Natural – Weather, natural disasters, or disease
- Infrastructure – damaged or blocked routes, loss of CIPs (Critical Infrastructure Points)
- Information – break down of communications means
Please note that the term “operational” can be used by civil as well as military actors tailored to their approach. Additional threats can arise during the operation phase and not every threat has to be.
In most theatres the following matrix is well established:
Example for scenario in Theatre XY:
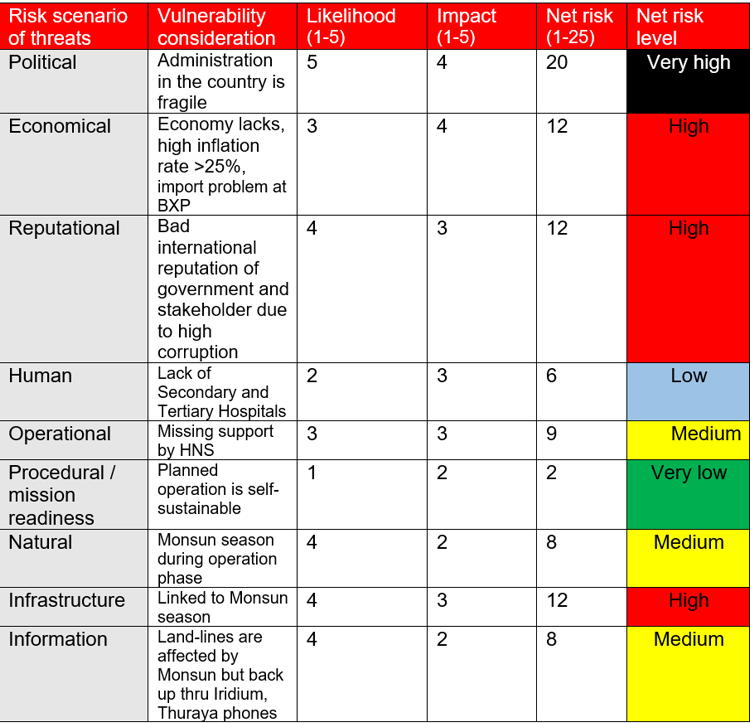
- *Normal case more than one vulnerable consideration does exist per risk threat. These have to be merged rated to one generic statement.
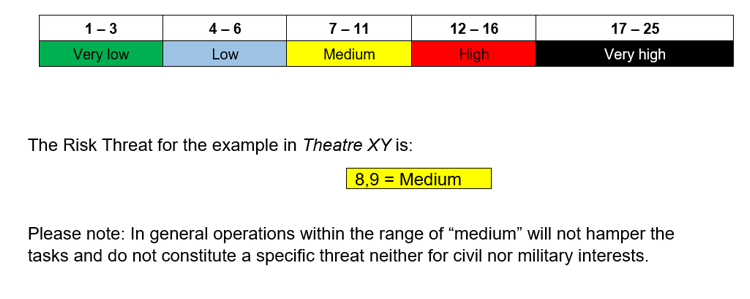
Net Risk (likelihood X impact):
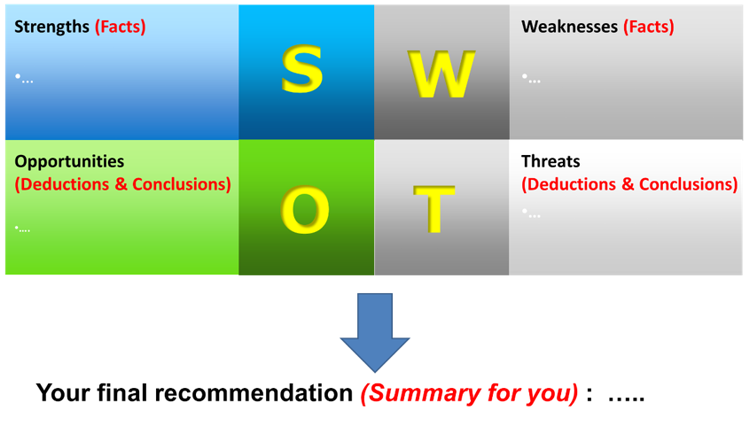
SWOT Analysis
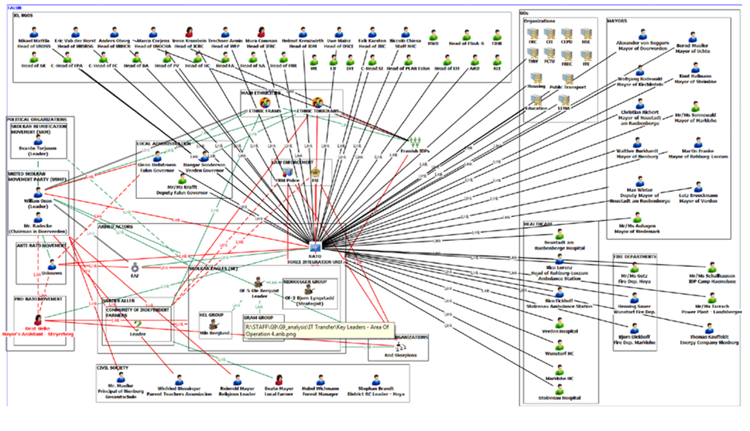
Actors diagram
CIMIC sites of significance
CIMIC SITES of significance (Abstract of an Annex W)
1. General. Sites within this category are not to be targeted without prior authorisation from COM ECISAM. Additional sensitive sites identified on the ground should be reported up through the Chain of Command.
2. Sites of Major CIMIC Significance (SMCS). These sites are of such cultural, either religious, or civil infrastructure significance that their destruction or damage would either:
- Potentially undermine the Force’s image.
- Seriously threaten the post-operation recovery of the involved countries.
- Inflict widespread and indiscriminate impact on key civil life support factors that would affect the civil population.
- Following sites can be deemed SMCS:
- Power plants/substations;
- APOD/SPOD, main LOCs and transportation networks;
- Water treatment/processing and distribution plants/installations;
- Dams and reservoirs;
- Hazardous industrial and commercial installations (Chemical or nuclear);
- Key historical/cultural or religious monuments or sites;
- UNESCO sites;
- IO/GO/NGO sites (i.e. IDP and Refugee camps).
3. Sites of CIMIC Significance (SCS). These sites are to have additional consideration prior to engagement, as engagement may: alienate significant elements of the civil population; adversely affect key civil life support; impede post-operation recovery of the concerned countries. The following sites can be deemed SCS:
- Places of worship;
- Community-based civil admin infrastructure (town hall, community centres);
- Health sites (hospitals, clinics, emergency service capability);
- Water sites (smaller scale distribution networks and infrastructures);
- Power lines (town/city power distribution lines);
- Sanitation (town/city sanitation processing capability);
- Cultural sites of historical and/or religious importance.
4. Reporting Newly Identified Sites. Formations and assigned units will identify and report new sites to JTF HQ J9 CIMIC for inclusion into the CIMIC sensitive sites list by providing grids (UTM, LATLONG and MGRS) and description of the site. The following are current sites identified as SMCS and SCS:
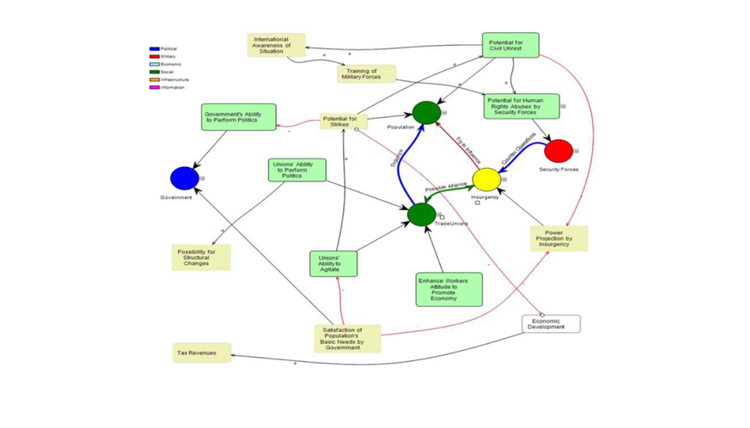
System analysis
Systems Analysis is an analytical process that can be employed to holistically examine adversaries, potential adversaries, non-aligned and cooperative nations or entities. It considers the operational environment as a set of complex adaptive systems in order to identify behaviors, structures and interrelationships, and to assess strengths, weaknesses or vulnerabilities.
It is successfully utilized in both the civilian and military communities and has proven to be particularly useful in analyzing and understanding problems in complex operational environments.
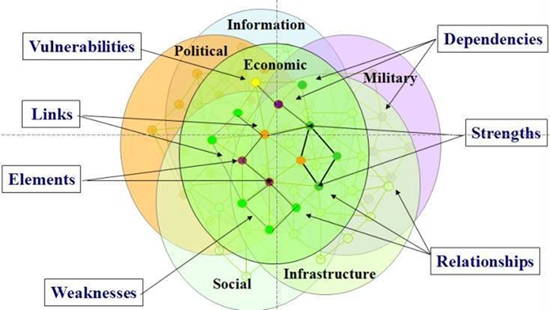
Systems Understanding
Systems Analysis aims to identify a network of systems and system elements, to identify the relationships and interactions between these system elements, and to create actionable knowledge to achieve a desired effect. This actionable knowledge can be used to target actions in order to attempt to affect capabilities, behavior, or interaction and influence of key actors and entities within the operational environment.
Systems Analysis integrates the analyses from work done on specific independent systems, such as the PMESII domains. Systems Analysis is a continuous, iterative and collaborative process that should be conducted in close co-operation with internal/external Subject Matter Experts (SMEs), governmental agencies, non-governmental organizations and Centres of Excellence (COEs), as required.
Systems Analysis supports the planning, execution, and assessment processes at the political, strategic, operational, and tactical levels. It describes the engagement space in varying degrees of complexity commensurate with the respective current level of NATO interest and is directly dependent on the analytical requirements. For example, a tactical view of a particular area within the engagement space will likely require more detailed study than a strategic view of the same area. The resulting in-depth understanding of the engagement space allows the Commander to determine what actions will produce changes in the behavior of critical actors in a way that will ultimately lead to the achievement of mission objectives.
The overall goal of Systems Analysis is to gain a comprehensive understanding of the dynamics, capabilities, behavior and interaction of the various systems (and their related subsystems) within the engagement space. As these elements evolve or change in time and space, Systems Analysis assists in providing a contextual assessment of the objectives, capabilities, likely actions and possible effects of each of these systems.
The iterative Systems Analysis process generally includes the following activities:
- Systems break down, in which subsystems, system elements and components are identified and where system boundaries, structures, and general relationships are determined.
- Interaction analysis, which explores inherent system dynamics in order to understand the underlying behavior of the system over time and highlighting the “cause and effect” relationships between elements of the system.
- Model synthesis, which re-combines the system’s elements to achieve a comprehensive understanding of the behavior of the system as a whole. This helps to identify similarities, interfaces, patterns, key factors, and feedback loops within the system in order to understand its comprehensive behavior.
The Systems Analysis process consists of the following activities and, as it is not a linear process, they may be re-iterated non-sequentially:
- Identify actors and their attributes, such as objectives, intentions, capabilities, relationships and interactions.
- dentify real world objects (e.g. a bridge) and abstract objects (e.g. a political power gap), processes and logical dependencies (e.g. bridge on Main Supply Route also provides access route for local trade and communal worship).
- Identify normative behavior and apply, where possible, available conceptual patterns.
- Identify potential knowledge gaps.
- Identify leverage points.
- Identify possible undesired effects from potential actions
To assist in the understanding of how a particular system operates, Systems Analysis frequently uses Influence Diagrams to help visualize how key actors (individuals, groups and organisations) interact with each other and which interrelationships are particularly important. Influence Diagrams can be used to show where critical requirements, capabilities or vulnerabilities exist and where the behavior of system elements can be influenced or affected in either a positive or negative way. These diagrams can also depict Objectives, Criteria for Success and Decisive Points.
The lack of availability of simulation tools and analysis time may significantly limit this phase of the analysis and thus restrict analysis of the dynamic aspects of the engagement space. The effort to develop a system analysis model could vary significantly depending on the method used, the time available and the desired level of fidelity/accuracy. In some cases, a Rehearsal of Concept (ROC drill) or war-gaming might adequately serve the purpose. For longer-term analysis, a number of simulation runs or a complete empirical study might be more appropriate.
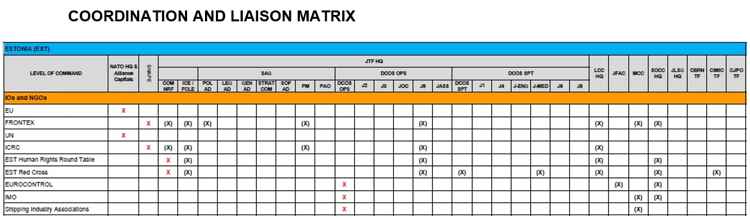
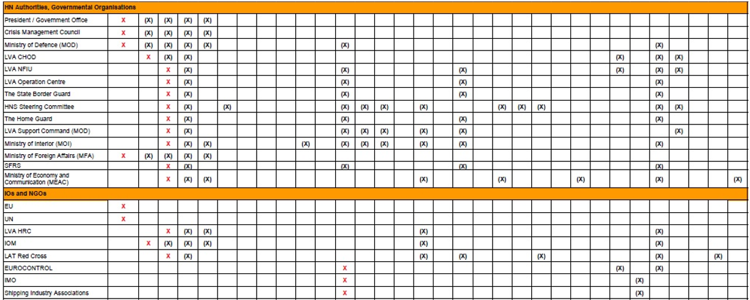
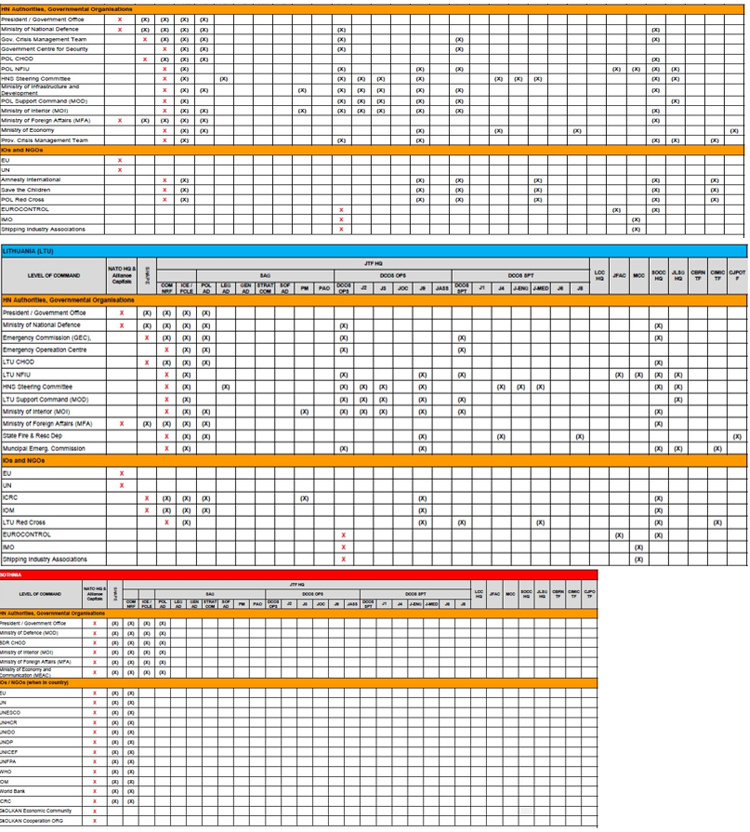
LIAISON AND COORDINATION MATRIX
1. General.
The Coordination and Liaison Matrix is a tool, drafted and maintained by CIMIC, for the use of JFCNP and CCs in the conduct of Civil and Military Interaction (CMI); engagement and liaison activities. Whilst the Matrix is maintained by CIMIC, all functional areas within the HQ are to input into the accurate identification of actors in the JOA and who, within NATO, they should interact with, and at what level: strategic, operational, tactical. All engagement and liaison activity requires synchronization with all other Information Activity (IA) and should be conducted IAW the COM's priorities and with adherence to the StratCom narrative.
2. Strategic Level Engagement.
External coordination efforts with regional non-NATO governments, the UN, EU and other IO/NGO/GO, as depicted in the Liaison Matrix, will be conducted through NATO HQ and by NATO capitals.
3. Operational Level Engagement.
It is planned and managed via the Engagement Working Group (EWG), synchronized with other IA in the IA Working Group (IAWG), for presentation at the Joint Effects information Board (JEIB). COM NRF is authorized by SACEUR to liaise and engage with HN representatives. In addition, SACEUR has authorized COM NRF, through HN coordination, to establish liaison with the IO/NGO/GO as depicted in the Coordination and Liaison Matrix.
4. Operational Level Liaison.
It is to be conducted IAW the Coordination and Liaison Matrix, which may include CMI across all functional areas; CIMIC, PAO, Info Ops, PSYOPS, ENG etc., and needs to be synchronized with other IA in the IAWG, for presentation at the JEIB.
5. Tactical Level Liaison.
Based on COM NRF’s liaison authority, CCs will establish and maintain tactical level liaison and coordination, as necessary, with the HN on the regional level and below. Liaison and coordination with IO/NGO/GO should be conducted IAW the Coordination and Liaison Matrix.
6. Matrix Legend
- Indicates lead on coordination, liaison and engagement.
- Indicates coordination, liaison and engagement at the relevant level of responsibility after approval of lead